If your reading this your wordpress instalation got hacked again. This article focuses on shell exploits. Here is a list of possible infected files that might have ended up on your server
detector.php ; inbox.php ; life.php ; newfile.php ; mailerz.php ; mars.php ; po.php ; prpup.php ; xmlrpc.php ; external_6c542970c2756c7225c0fec13f98b9e4.php
These files are not the work of a single hacker, but rather the collective work of some multiple hackers that used the same exploit. I will discuss each and every file, but first of all, lets talk about how your wordpress install got hacked.
Usually its the good old timthumb.php exploit. TimThumb is a picture resize script that can allow a hacker to upload a “shell” on your server. The first thing you can do is search for timthumb on your server and update it to TimThumb version : 2.8.10 .
Anything below that and you will get hacked again and again.
One thing you can do to prevent this are : use your favorite ftp client to connect to you server, (for me is filezilla) go to server -> force showing hidden files then edit your .htaccess file and include these lines right at the top of the file (remove the space before files and /files) :
< files wp-config.php>
order allow,deny
deny from all
< /files>
# Block the include-only files.
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ - [F,L]
RewriteRule !^wp-includes/ - [S=3]
RewriteRule ^wp-includes/[^/]+\.php$ - [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+\.php - [F,L]
RewriteRule ^wp-includes/theme-compat/ - [F,L]
Another is always use the latest version of wordpress, and always check that folders are set to 755 and files to 644 (chmod); also backup as often as you can, and change all passwords wordpress admin, ftp, mysql since the hacker once he managed to run a shell saw all your passwords .
Now lets discuss the infected files : (there is no easy fix for this, you have to check your logs and look for the tale-tale signs of hacking , then remove those files and just to be sure replace them with black chmod 444 ones )

Usually just checking the date of creation of the files will set you on the right direction to what files are infected. (hacked files will have a newer creation date than the normal files)
1. external_6c542970c2756c7225c0fec13f98b9e4.php
this is the file used to notifie the hacked that you use an old timthumb script. the file has a gif header. this is how the file looks like

adn this is what it translates to
so this file is used to create a newfile.php on your server. simple as that ! the full code is here external_6c542970c2756c7225c0fec13f98b9e4.php
2. newfile.php
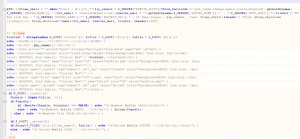
this is the “shell”, what that means is a filemanager . this is what’s in the header of the file
?php # Don Tukulesto
$auth_password = "";/*
$color = "#df5";
$default_action = 'FilesMan';
$default_use_ajax = true;
$default_charset = 'Windows-1251';
the code in the file is pretty big 61k so i’ll post it here newfile.php
the password for this shell is foot12
ever wonder how a shell looks like (what the hacker can access) ? this is called PHP jackal 1.9

Once he was able to do this, you kinda need to change every password related to you site, you can think of …
3. mars.php
I was not able to decrypt this file the source is here, any help would be appreciated, i know it’s a shell .
4. po.php also a shell the password for this one is dilly
/*||||||||||||||||||||||||||||||||||||||||||*/
# ibl13Z Private Shell |
# Forums: hxxp://indonesiancoder.com |
/*||||||||||||||||||||||||||||||||||||||||||*/
i was able to decode it, however i cannot post it to pastebin.
5. detector.php and xmlrpc.php WSO 2.1 (Web Shell by oRb) the password for this one is root. detector.php is the obfuscated version of xmlrpc.php.
the code looks like this xmlrpc.php
This is how the interface looks like.

6. mailerz.php is an spam bot this is the code of mailerz.php
some code from that file
?php
//your real email address needs to go below
$secure = "chairo335123@gmail.com";
@$action=$_POST['action'];
@$from=$_POST['from'];
@$realname=$_POST['realname'];
7. inbox.php also a spam bot username and password is tbt . original file source for inbox.php
Mailer Inbox - ALsa7r
ALsa7r is the sandmonkey who designed one of the exploits (webshell+spam bot) as he so gracefully explains some other hacks on his youtube channel.
8. prpup.php is a hijacker page, it redirects to another infected site that has some phising page set-up.
I know that some people might think i’m crazy for posting all the tools that hackers use, but understanding how they work might set you in the right direction in how to better secure your site !
I will add more details as things evolve :)
Author : Joey V. (IP: 86.120.216.220 , 86-120-216-220.rdsnet.ro)
E-mail : fuvik_200tms@ashz.com
URL :
Whois : hxxp://whois.arin.net/rest/ip/86.120.216.220
Comment:
Outstanding…. and dangerous. Thx 4 the info. U rock. Ur instructions are very easy to follow, u should think about starting a course or smth to teach others wp for advanced dummies. Nice stuff.
__________________________________________________________________________________________________
My answer to you, my friend, is this :
wanting to fuck me 200 times, shows somewhat of a homosexual tendency. I for one, do not wish to engage in any homosexual activities, be it with you (raging homo) or any other person out there. Thank you for your comment.
Your activity has been logged, have a nice day !
Hey Victor,
Thanks for the explanation. ALL my sites (15 of them) were hacked using this method recently. Once they gained access to one, they had access to all of them.
This is the only thing I hate about wordpress.
Thanks for the explanation.
D
Glad I could set you in the right direction. To be honest, the only way i found so far, to keep wordpress safe, is to fully cache every article on the site then set everything on “lock-down” (using wordpress super cache for example) and then break the wordpress install (just break the config file). The effect is super nice, all the files on your site will be served from the cache, so any alterations that the hacker might do to your site will not reflect on all pages (since he no longer has access to header.php of footer.php, since all in chached, he will only be able to edit one file at a time). Then, if you get hacked, all you need to do is fix the config file, and delete the cache. This is the worse solution, but it works like a charm.
Yes I’m reading this coz I got hacked :-)
So far I’m with you 100% – learned more through this page than all the others that I’ve read so far. Many thanks.
One question that I’d like cleared up if you would be so kind. Editing the htaccess – so far mine says the following, what I would like to know is EXACTLY where I add your extra lines.
# BEGIN WordPress
RewriteEngine On
RewriteBase /
RewriteRule ^index\.php$ – [L]
RewriteCond %{REQUEST_FILENAME} !-f
RewriteCond %{REQUEST_FILENAME} !-d
RewriteRule . /index.php [L]
# END WordPress
Sorry to hear that Snail… It makes no difference where you add them (before or after) just make sure you remove the space before /files and don’t insert the
RewriteEngine On
RewriteBase /
as you already have them.
Cheers !